Iseehear Information Security Management policies were established in order to protect our subscriber's Data, Intellectual Property, Privacy, as well as address Iseehear's IT Security, Risk Management, Research Continuity and Support Services.
All Iseehear cloud applications are supported by a robust Information Security Management and Data Governance structure that addresses Iseehear's application and IT infrastructure security, risk management policies, disaster recovery policies and research continuity policies.
To learn more about Iseehear Information Security Management (ISM) and some of the security resources we have deployed, please use the menu links illustrated in the examples below to review the security related services and policies that we provide.
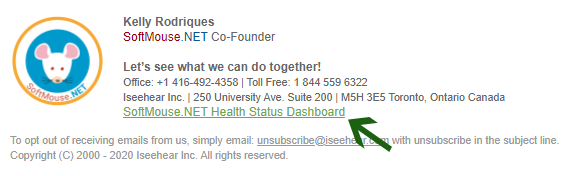
Example 1, is an illustration representing an email signature link that can be located in our corporate emails.
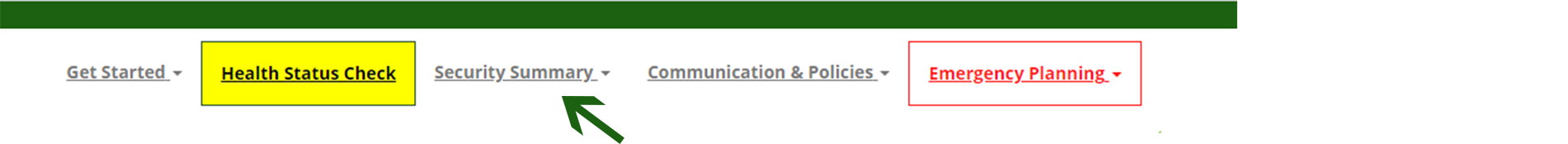
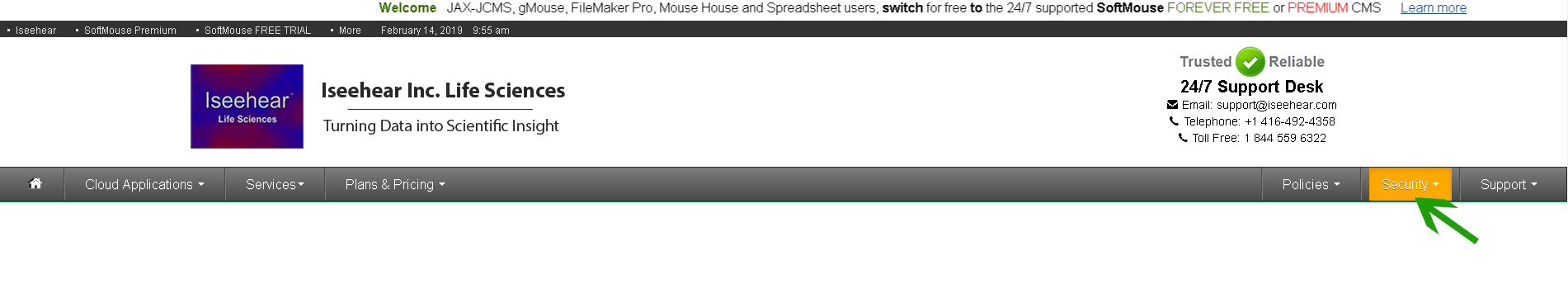
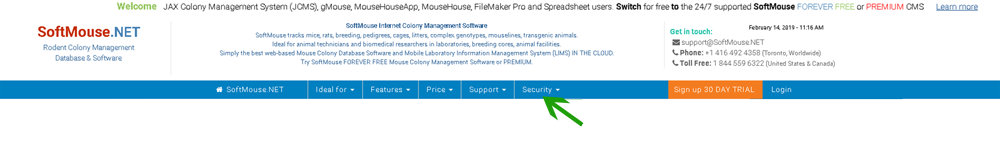
Examples 2, 3 and 4 are illustrations of links that can be found in the menus of our main websites.